You may be asking yourself is the Zero Trace Pen necessary?
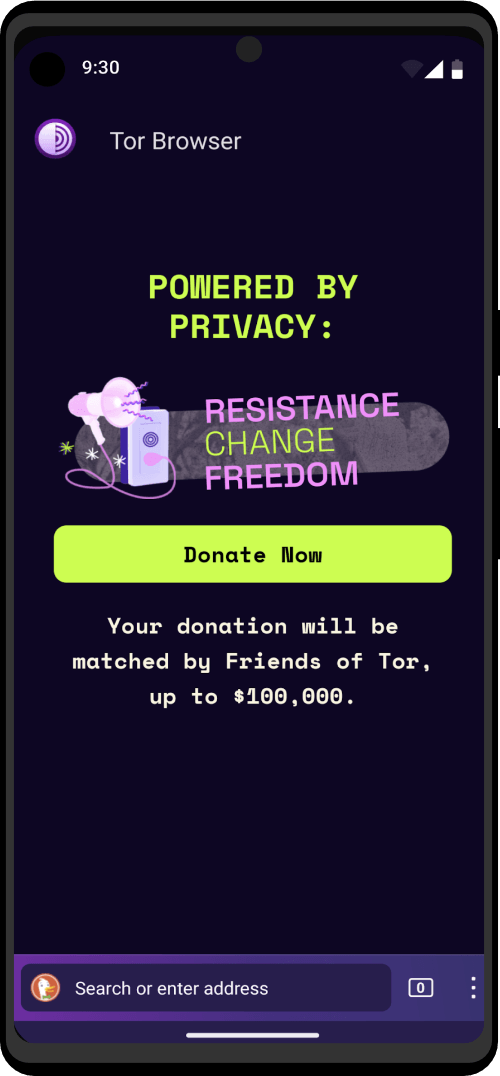
YES. Even if you think you are nobody and no one has any reason to surveil you, you should not be using the Tor browser on a regular operating system like Windows or macOS.
Let me give you an example: Let’s say you utilize the Tor browser within a Windows OS environment to place a questionable online order and everything seems to go fine. However, unfortunately, your package gets caught by customs because the seller did not package it correctly.
Now the authorities begin to investigate because someone tried to send questionable items to you. One possible consequence is that they will deliver the package to you but raid your house shortly afterward because you are in possession of said items. (This is called a controlled delivery.)

Since Windows is not secure, they will find all the evidence they need to prove that you were the one who placed the order. You would not have these issues with on the Zero Trace Pen because nobody can say what you did on it or access the files you stored on your persistence volume. The Zero Trace Pen does not even leave a trace that it was booted on your PC!
So as you can see, The Zero Trace Pen is not only to prevent you from getting your privacy infringed but it’s also great at minimizing your risk exposure if you get investigated.
Do I need a VPN alongside the Zero Trace Pen?
Normally, no.
Here is an excerpt from one of our head developers about VPNs:
Some users have requested support for VPNs in the Zero Trace Pen to “improve” Tor’s anonymity. You know, more hops must be better, right?. That’s just incorrect – if anything VPNs make the situation worse since they basically introduce either a permanent entry guard (if the VPN is set up before Tor) or a permanent exit node (if the VPN is accessed through Tor).
Similarly, we don’t want to support VPNs as a replacement for Tor since that provides terrible anonymity and hence isn’t compatible with the Zero Trace Pen’s goal.
I’m probably suspecting you want to use a VPN to be able to hide your tor usage from your ISP and/or add another security layer.
Here’s what you can do instead:
- If you want to hide your Tor usage from your ISP, then you can select the “More Options” button on the Zero Trace Pen greeting screen and then select the option “This computer’s Internet connection is censored, filter or proxied”. However, if you are not living under an oppressive regime in which it is illegal or not possible to use Tor normally, it is not recommended to use that option since it only takes away resources from people who really need them.
There are many other OpSec factors that are more important and have a greater impact on your well-being, so please take care of them first before using the Zero Trace Pen with a VPN.
If you still want to use Tor and a VPN, please read the designated section regarding this setup.
Ordered without the Zero Trace Pen before?
If you did not use the Zero Trace Pen for previous questionable activities you made a mistake. The problem is not that much that 3rd parties will have traces of your online activity to follow, but rather that if you get in trouble later they can still find proof of your past activities and then link it all back to you. Therefore, it is important to remove the evidence immediately and step up your OpSec for future endeavors.
The first step is to uninstall all the tools you used to place an order on your insecure Windows or macOS. That includes the Tor browser, PGP tools, and Bitcoin wallets, . . .
After that, you have to overwrite the free disk space on your hard drive. This will make it harder to recover the deleted tools. That means the uninstalled tools will need to get overwritten.
Note: this is not 100% secure. There are always log files that your insecure OS might have created that still show that you utilized these tools (e.g. PGP tools). Therefore it is important that you follow the steps mentioned above and keep everything related to these activities on the Zero Trace Pen in the future.
Using the Zero Trace Pen on a personal/work computer
Using the Zero Trace Pen on a computer doesn’t alter or affect the main operating system installed on it. This allows you to freely use it on your computer, a friend’s computer, or one at your local library. After shutting down the Zero Trace Pen, the computer will start again with its usual operating system.
The Zero Trace Pen is configured with special care to not utilize the computer’s hard disks, even if there is some swap space on them. The only storage space used by the Zero Trace Pen is in RAM, which is automatically purged when the computer shuts down. So not to worry, you won’t leave any trace on the computer either of the Zero Trace Pen system itself or what you used it for. That’s why we call the Zero Trace Pen “zero trace”.

This allows you to work with sensitive documents on any computer and protects you from data recovery after shutdown. Of course, you can still explicitly save specific documents to another external hard disk and store them for future use.
tl;dr you can use the Zero Trace Pen on your normal computer and do not have to buy a burner laptop.
Using the Zero Trace Pen on your own WiFi
If you use the Zero Trace Pen (or Tor in general) on your own WiFi, your ISP will only know that you are using Tor but not what you are doing exactly. If you do not want your ISP to know that you are using tor you can tell Tor to use bridges on the Zero Trace Pen greeting screen (select “Yes” for the more options question and after pressing forward select the “My computer’s Internet connection is censored, filtered or proxied” option).
That will obfuscate the fact that you are using Tor from your ISP. Although, it is not necessary as long as you are not living under an oppressive regime that blocks Tor and/or makes the use of it illegal. If that is not the case, please do not use bridges as it would take away resources from people who actually need them.
Furthermore, the only reason for using another WiFi other than your own is that an attacker would not get your real IP address in case of a de-anonymization attack. However, these attacks are unrealistic for the majority of users and the risks that this method brings along (e.g. someone shoulder-surfing or a camera recording your face and/or screen) might not be worth it. Therefore using your own WiFi along with following all the other tips, is a much better solution.
Is it okay to use a WiFi with login?

Sometimes you will have to log into WiFis with credentials – that in some cases are also tied to your real identity (e.g. a college WiFi). the Zero Trace Pen spoofs all MAC addresses by default, which means that a system administrator would only see that a another device other than your default one; logged in with your credentials. That adds some plausible deniability because you can claim that someone stole your login credentials and logged in with them on another computer.
Additionally, nobody knows what exactly you are doing since the whole internet traffic that the Zero Trace Pen produces is routed through the Tor network and is therefore encrypted and nobody has access to where it connects. So to make it short: yes you can use the Zero Trace Pen on a WiFi that requires you to log in.
Are DNS leaks an issue?
When using Tor, your computer does not make the DNS requests for the sites you visit, but the exit node does (the last node in the chain of relays that route your Tor traffic). This makes the DNS requests for you. Tor only supports TCP not UDP traffic. So when using the Zero Trace Pen, which routes all your traffic through the Tor network, you will not have to worry about it.
Is running the latest version of the Zero Trace Pen necessary?
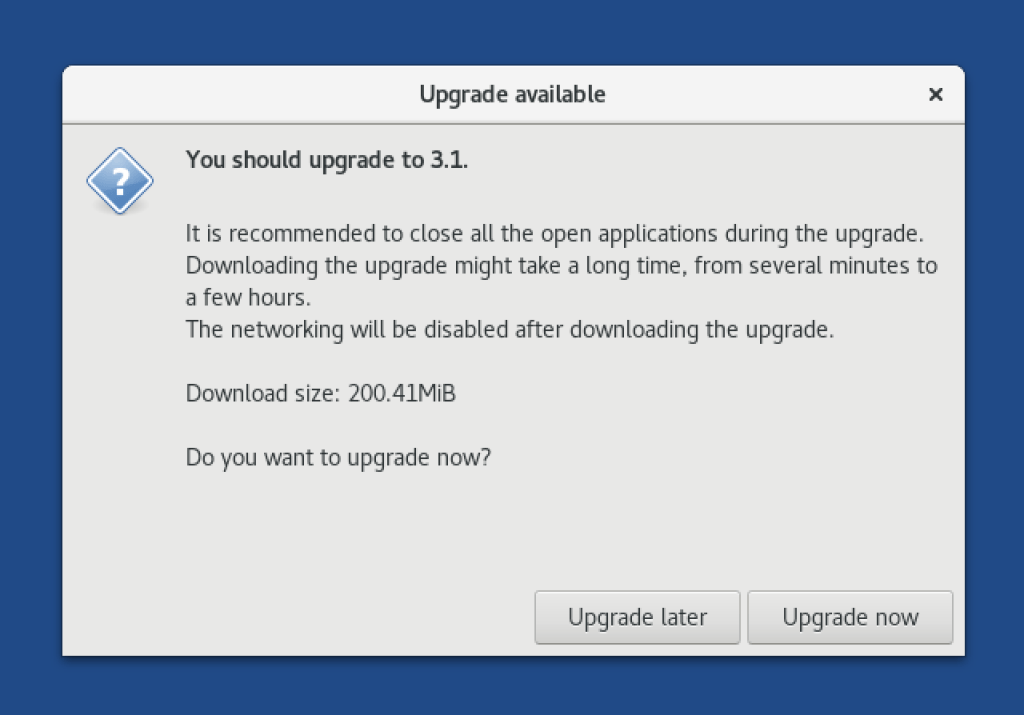
Yes. It is absolutely crucial that you always use the latest version of the Zero Trace Pen since the updates usually fix security vulnerabilities. So take a few minutes and upgrade the Zero Trace Pen as soon as you get the notification that an update is available.
Why is JavaScript enabled globally by default and the security slider set to low?
There are a lot of not so tech-savvy Zero Trace Pen users who would have a hard time dealing with all the different settings if they were all set too high. Therefore we decided to set the default settings to not-so-strict values to make the Zero Trace Pen experience better for these users.
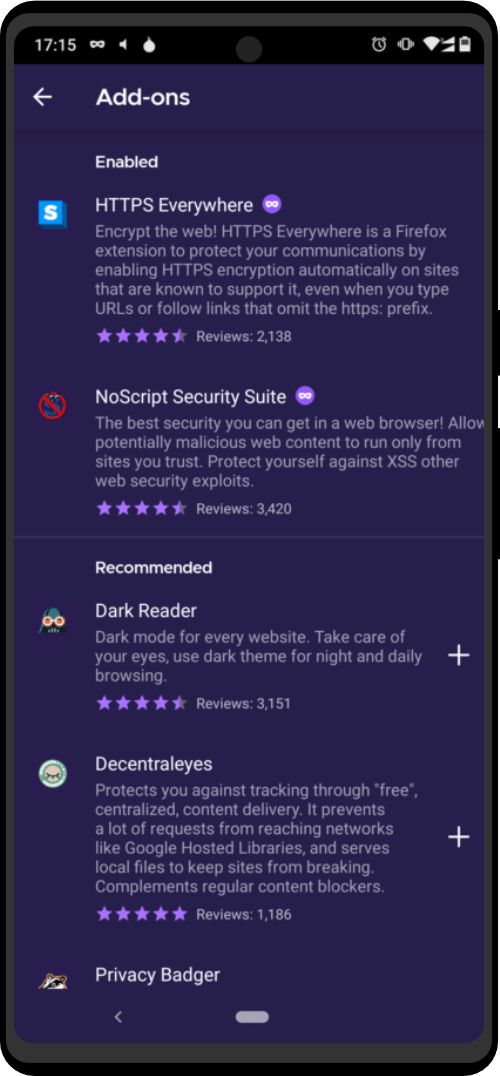
For performing questionable activities, you should make sure that you set the security slider to high every time you start the Tor browser.